Fortify Your Business with
Way2Protect's Ultimate Cybersecurity Shield
Transform cybersecurity from a challenge into your competitive advantage.
Fortify Your Business with Way2Protect's Ultimate Cybersecurity Shield
Transform cybersecurity from a challenge into your competitive advantage.
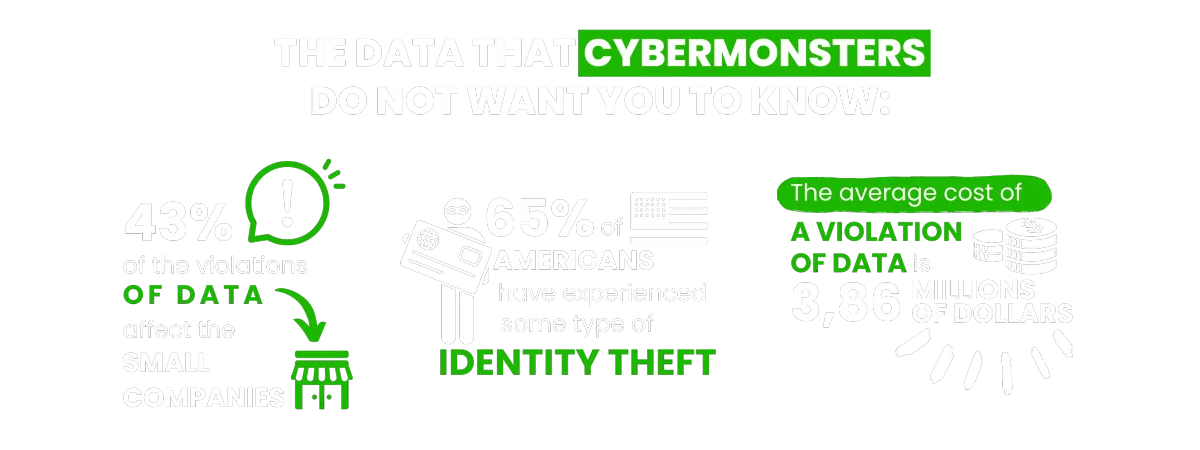
You find these and other figures in my book Happily Ever Cyber and on Cisa.gov

Find out how to push Cybermonsters away from your private data
With tips to help prevent a cyber attack protecting your family, work environment and yourself:
AS SEEN ON:

Find out how to push Cybermonsters away from your private data
With tips to help prevent a cyber attack protecting your family, work environment and yourself:
AS SEEN ON:
Push Cybermonsters away from your private data.
Subscribe to my newsletter about cybersecurity and cyber safety. New issues every Tuesday.

Push Cybermonsters away from your private data.
Subscribe to my newsletter about cybersecurity and cyber safety. New issues every Tuesday.

Protect those that matters most to you:

Family
Protect your child(ren), teens,
and your parents.

Business Owners
Protect your data, your customer's information, your employees,
and your brand!

Yourself
Have peace of mind online!
International Bestselling & Award-Winning Cyber Safety Author
Identity theft & cyber crime can happen to anyone.



Why choosing us?
In a world full of digital distractions, we understand the importance of cultivating a healthy balance. At Way2Protect, our mission is clear: to be your trusted guide to a conscious and protected online experience, both for you and for what you value most: your family, your business, and your peace of mind.
Way2Protect becomes your fundamental ally in your digital world, providing you with hassle-free security and adapting cybersecurity practices to your routine without sacrificing your time. We facilitate the process, guiding you in the implementation of effective cybersecurity practices to protect your family, your business, and your work teams.
Why choosing us?
In a world full of digital distractions, we understand the importance of cultivating a healthy balance. At Way2Protect, our mission is clear: to be your trusted guide to a conscious and protected online experience, both for you and for what you value most: your family, your business, and your peace of mind.
Way2Protect becomes your fundamental ally in your digital world, providing you with hassle-free security and adapting cybersecurity practices to your routine without sacrificing your time. We facilitate the process, guiding you in the implementation of effective cybersecurity practices to protect your family, your business, and your work teams.

Get the latest news in the Cyber Security World

5 Common Cybersecurity Risks You Face When Traveling and How to Protect Yourself
1- Public Wi-Fi: The Hidden Danger
Imagine this: You’re sitting at a coffee shop, sipping your latte and browsing the web on the free Wi-Fi. But did you know that hackers can easily intercept your data and steal your personal information on public Wi-Fi? Don’t worry, there’s a simple solution. Keep reading.
Using public Wi-Fi can be convenient, but it comes with certain risks. Cybercriminals often target public Wi-Fi networks because they are generally unsecured and easy to access. This can make it easy for them to intercept your internet traffic and steal your personal information. That’s why it’s important to take steps to protect yourself when using public Wi-Fi networks.
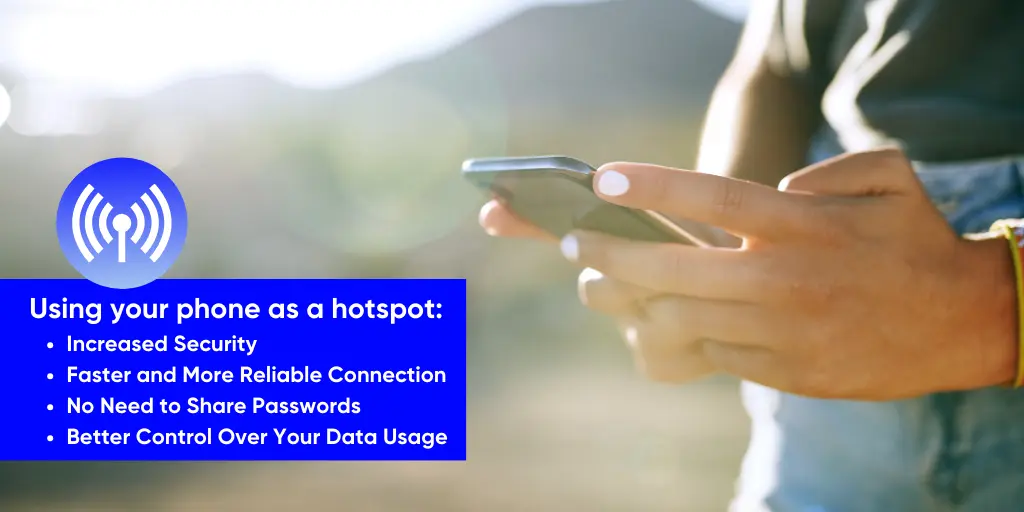
One way to do this is by using your phone as a hotspot instead of connecting to public Wi-Fi. A hotspot is a feature on your phone that allows you to share your cellular data connection with other devices. When you use your phone as a hotspot, you are connecting to the internet using your cellular data plan instead of a public Wi-Fi network. This can provide you with a more secure connection and protect your personal information from being intercepted by cybercriminals.
Here are some reasons why using your phone as a hotspot is a good idea:
Increased Security
When you use your phone as a hotspot, you are essentially creating a private Wi-Fi network that only you can access. This means that your internet traffic is not visible to anyone else, and your personal information is less likely to be intercepted by cybercriminals. Cellular data connections are generally more secure than public Wi-Fi networks because they use encryption to protect your data.
Faster and More Reliable Connection
Public Wi-Fi networks can be slow and unreliable, especially if there are many people using the same network at the same time. When you use your phone as a hotspot, you are accessing the internet using your cellular data plan, which can be faster and more reliable than public Wi-Fi networks.
No Need to Share Passwords
When you connect to a public Wi-Fi network, you often have to enter a password or other credentials to access the network. This means that you are sharing your personal information with the network, which can be risky. When you use your phone as a hotspot, there is no need to share passwords or other credentials, which can help protect your personal information.
Better Control Over Your Data Usage
When you connect to a public Wi-Fi network, you often have to share your data usage with the network. This means that the network can track your internet usage and potentially use your data for advertising or other purposes. When you use your phone as a hotspot, you have more control over your data usage, and you can monitor how much data you are using.
In conclusion, using your phone as a hotspot can be a good idea if you want to protect your personal information and ensure a secure and reliable internet connection. While public Wi-Fi networks can be convenient, they come with certain risks, and using your phone as a hotspot can help mitigate those risks. Always remember to keep your phone and hotspot password protected and updated with the latest security updates to ensure the highest level of protection.
If you must use public WiFi then make sure you include a Virtual Private Network (VPN) or avoid using public Wi-Fi for sensitive transactions such as banking, shopping, or logging into personal accounts. Also avoid updating your phone and changing your passwords over a public WiFi.
A VPN encrypts your internet traffic and routes it through a secure server, making it much harder for Cybermonsters to intercept your data. If you don’t have a VPN, at the end of the article, I will share my favorite VPN tool.
2- Unsecured Devices: The Trojan Horse
When traveling, you remember you have to print a document and you need to send an email and you are heading into the business center, ready to login into your account. WAIT!!!
Using unsecured devices such as hotel computers or public kiosks to access the internet, your personal accounts or your email can put you in danger. You don’t know if the devices are updated or if they are infected with malware that can leave you vulnerable to cyber-attacks. Be intentional and avoid using these devices for sensitive activities such as banking or logging into personal accounts.
Unsecured devices are a common threat to travelers, as they can be infected with malware that can steal your personal information or even take over your device. This can happen even if you’re just browsing the web or checking your email.
To protect yourself from this Trojan Horse, it’s best to avoid using unsecured devices for sensitive activities such as banking or logging into personal accounts. If you must use an unsecured device, make sure to log out of all accounts when you’re done and clear your browsing history and cache.
3- Phishing Scams: The Art of Deception
Phishing scams are a common tactic used by cybercriminals to steal personal information from unsuspecting victims. Be extra vigilant against these types of scams when traveling. Be Intentional, Aware and Mindful and never click on unknown links or download attachments from unfamiliar emails.
Phishing scams can take many forms, from fake emails that ask you to update your password to fake websites that look like the real thing. These scams are designed to trick you into revealing your personal information, such as usernames, passwords, or credit card numbers.
To protect yourself from this art of deception, it’s best to be extra vigilant against phishing scams when traveling. Never click on unknown links or download attachments from unfamiliar emails. If you’re unsure about an email or website, it’s best to err on the side of caution and avoid it altogether.
4- Physical Theft or Loss of Devices: The Nightmare Scenario

Picture this: You’re on a train, traveling to your next destination, and suddenly your phone or laptop is stolen. Your heart sinks as you realize that all of your personal and financial information is now in the hands of a thief. This nightmare scenario can happen to anyone, but there are steps you can take to prevent it from happening to you.
To protect yourself from physical theft or loss of devices, it’s best to keep your devices with you at all times, or locked away in a secure location. Use strong passwords and enable device tracking and remote wipe features. Make sure to back up your data regularly to prevent loss in case of theft or loss.
5- Social Engineering: The Manipulation Game
Social engineering is the art of manipulating people into divulging personal or confidential information. This can happen through phone calls, emails, or even face-to-face interactions with strangers. Don’t fall for their tricks. Be skeptical and verify before giving out any personal information.
Social engineering attacks can take many forms, from fake calls claiming to be from your bank to fake hotel staff asking for your credit card information. These attacks rely on trust and manipulation to extract information from unsuspecting victims.
To protect yourself from social engineering attacks, it’s best to be skeptical and verify before giving out any personal information. Ask for identification and call the company or organization directly to confirm the request is legitimate. Don’t be afraid to say no or walk away from suspicious interactions.
In summary, traveling can be a wonderful experience, but it’s important to be aware of the cybersecurity risks you may face while on the road. By following these tips and taking a few simple precautions, you can help protect yourself and your personal information from cybercrime. Don’t let Cybermonsters ruin your adventure – stay safe and enjoy your travels!
You may also like to read :- Unlocking Email Security: 3 Foolproof Methods to Determine If an Email is Safe
What is a Data Breach? Understanding the Impact and Prevention
Understanding Privacy and Code of Conduct
Cloning Attack in Cyber Security types, Signs and Preventions
Live Happily Ever Cyber!
Sandra Estok
Subscribe for more ways to protect what matters most to you against hackers, scammers, and Cybermonsters™