Fortify Your Business with
Way2Protect's Ultimate Cybersecurity Shield
Transform cybersecurity from a challenge into your competitive advantage.
Fortify Your Business with Way2Protect's Ultimate Cybersecurity Shield
Transform cybersecurity from a challenge into your competitive advantage.
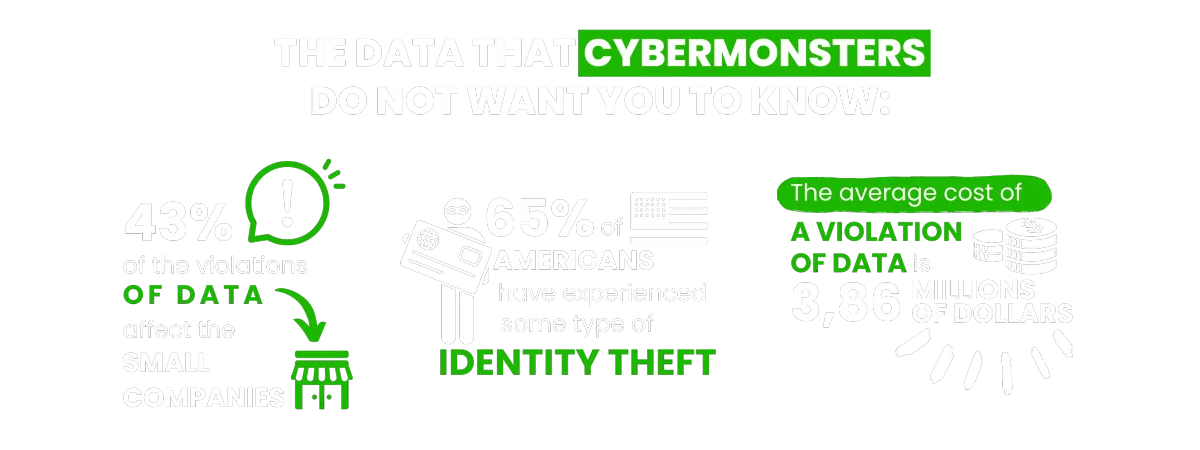
You find these and other figures in my book Happily Ever Cyber and on Cisa.gov

Find out how to push Cybermonsters away from your private data
With tips to help prevent a cyber attack protecting your family, work environment and yourself:
AS SEEN ON:

Find out how to push Cybermonsters away from your private data
With tips to help prevent a cyber attack protecting your family, work environment and yourself:
AS SEEN ON:
Push Cybermonsters away from your private data.
Subscribe to my newsletter about cybersecurity and cyber safety. New issues every Tuesday.

Push Cybermonsters away from your private data.
Subscribe to my newsletter about cybersecurity and cyber safety. New issues every Tuesday.

Protect those that matters most to you:

Family
Protect your child(ren), teens,
and your parents.

Business Owners
Protect your data, your customer's information, your employees,
and your brand!

Yourself
Have peace of mind online!
International Bestselling & Award-Winning Cyber Safety Author
Identity theft & cyber crime can happen to anyone.



Why choosing us?
In a world full of digital distractions, we understand the importance of cultivating a healthy balance. At Way2Protect, our mission is clear: to be your trusted guide to a conscious and protected online experience, both for you and for what you value most: your family, your business, and your peace of mind.
Way2Protect becomes your fundamental ally in your digital world, providing you with hassle-free security and adapting cybersecurity practices to your routine without sacrificing your time. We facilitate the process, guiding you in the implementation of effective cybersecurity practices to protect your family, your business, and your work teams.
Why choosing us?
In a world full of digital distractions, we understand the importance of cultivating a healthy balance. At Way2Protect, our mission is clear: to be your trusted guide to a conscious and protected online experience, both for you and for what you value most: your family, your business, and your peace of mind.
Way2Protect becomes your fundamental ally in your digital world, providing you with hassle-free security and adapting cybersecurity practices to your routine without sacrificing your time. We facilitate the process, guiding you in the implementation of effective cybersecurity practices to protect your family, your business, and your work teams.

Get the latest news in the Cyber Security World

How to Safely Open An Email Attachment
Email attachments can be a convenient way to receive files, photos, and documents from others. However, they can also pose a security risk if they contain viruses or malware. With the increasing number of cyber threats, it’s crucial to take necessary precautions when opening attachments in your email. In this blog post, we will discuss some simple yet effective tips to help you safely open an email attachment without putting your computer and personal information at risk
Growing up I used to watch Coyote and Roadrunner, and I always ended up irritated.
I used to wonder “Why doesn’t Coyote use his creativity and out-of-the-box ideas for something better than trying to trick Roadrunner? What a waste of talent!”
Did you ever watch these cartoons? Did you ever have this thought?
Cybermonsters act like Coyote every single day.
They will use elaborate email traps, including attachments and links with the intention to lure us.
They pretend to be legitimate financial institutes, government agencies, businesses, even our friends or relatives.
We become the “roadrunners” in the story, so we must always stay aware and mindful of our surroundings when it comes to our technology.
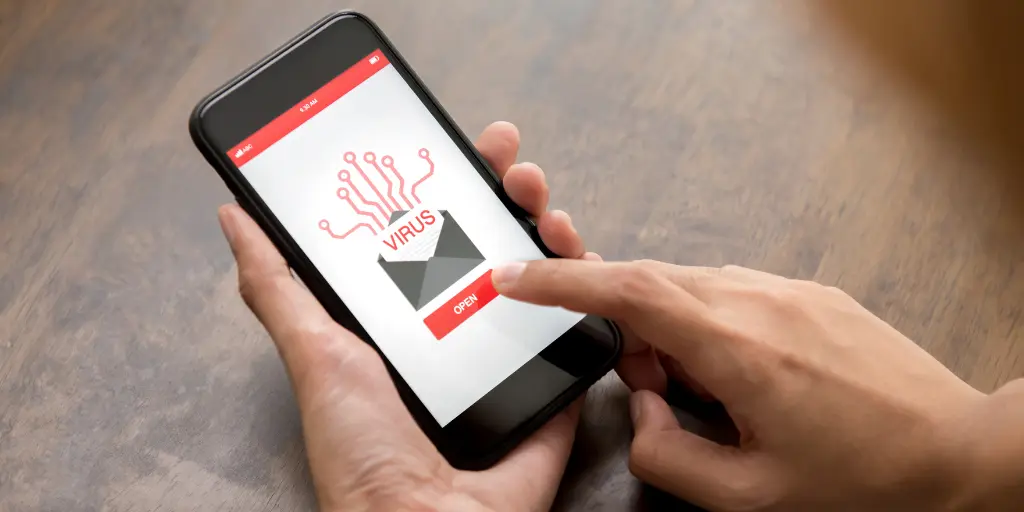
How do I know If An Attachment Is Safe?
What if you receive an attachment that really seems legit?
What if you are actually expecting an attachment?
How do you know if this time it IS real?
The Triple C Approach to Safely Open An Email Attachment

I use what I call the Triple C approach to validate attachments: Call, Check, Confirm.
Let’s go through each step so that you can be safe when you’re opening email attachments:
Call. Call the sender and validate that they actually sent the particular attachment you are about to open.
Check. Look at the end of the attachment extension to verify what type of file it is (you can find it at the end of the file). The most obviously dangerous extension is EXE, as it stands for “execute” and will install a program on your computer once you download it.
Sometimes we underestimate common extensions because we are so used to them, like spreadsheets, presentations, letter documents, and images.
Any of these types of files may contain hidden malware, so be aware and become more familiar with extensions such as XLS, PPT, PDF, DOC, IMG, ZIP, among many others.
Confirm. Make sure the attachment is safe using your antivirus program or online scanners before opening your file.
You can save the file on your computer (without opening it!) and then scan it. You can also use online virus scanning services.
I have used [email protected] by forwarding the email with the word SCAN on the subject line. They will check out your file and send you the scan results.
Next time you receive an email with an attachment, take a moment to pause and reflect on the 3 C’s. Once you do this mindfully a few times, it’ll become a habit that can protect you from many online Coyotes!
People also Asked
1. How can I check if a link is a virus?
To check if a link is a virus, you can use antivirus software or online virus scanners. You can also hover over the link to see the URL and check if it’s from a reputable source before clicking on it. Be cautious of links from unknown sources or ones that look suspicious.
2. Is it safe to click any link?
No, not all links are safe to click. It’s important to be cautious and verify the source of a link before clicking on it, especially if it comes from an unknown source or looks suspicious. Scammers and hackers often use links to spread viruses or steal personal information, so it’s important to be careful and use caution when clicking links online.
3. How do I know if a link is phishing?
To identify if a link is phishing, look for signs like:
1) URL does not match the name of the website you expect to visit,
2) the link takes you to a page asking for personal information,
3) page looks different from the usual login page,
4) the email sender is not familiar,
5) email has spelling or grammar errors, and
the link is sent from an unusual or unexpected source.
Be cautious and always double-check before entering any personal information online.
4. Can you get a virus just by opening a link?
Yes, it’s possible to get a virus by just opening a link if the link leads to a malicious website or downloads a harmful file. It’s important to be cautious when clicking on links, especially from unknown sources, and to have updated anti-virus software installed on your device.
5. What if I accidentally clicked on a suspicious link?
If you accidentally clicked on a suspicious link, you should immediately take steps to protect your computer and personal information. Here are some recommended steps to take:
Disconnect from the internet: If you suspect that the link you clicked on is malicious, disconnect your device from the internet to prevent the spread of any potential malware.
Scan your device: Use a reputable antivirus software to scan your device and detect any potential threats.
Change your passwords: Change the passwords for all of your online accounts, especially those that may contain sensitive information like financial accounts or email accounts.
Be cautious of any suspicious activity: Monitor your accounts for any unusual activity and immediately report any unauthorized transactions or activity.
Keep software up-to-date: Make sure that your operating system and all of your software are up-to-date to prevent vulnerabilities from being exploited by malicious actors.
How do you stay safe like the Roadrunner online? Share your strategies below!
You may also like to read :- 5 Common Cybersecurity Risks You Face When Traveling and How to Protect Yourself
Unlocking Email Security: 3 Foolproof Methods to Determine If an Email is Safe
What is a Data Breach? Understanding the Impact and Prevention
Understanding Privacy and Code of Conduct
Cloning Attack in Cyber Security types, Signs and Preventions
Live Happily Ever Cyber!
Sandra Estok
Subscribe for more ways to protect what matters most to you against hackers, scammers, and Cybermonsters™