Fortify Your Business with
Way2Protect's Ultimate Cybersecurity Shield
Transform cybersecurity from a challenge into your competitive advantage.
Fortify Your Business with Way2Protect's Ultimate Cybersecurity Shield
Transform cybersecurity from a challenge into your competitive advantage.
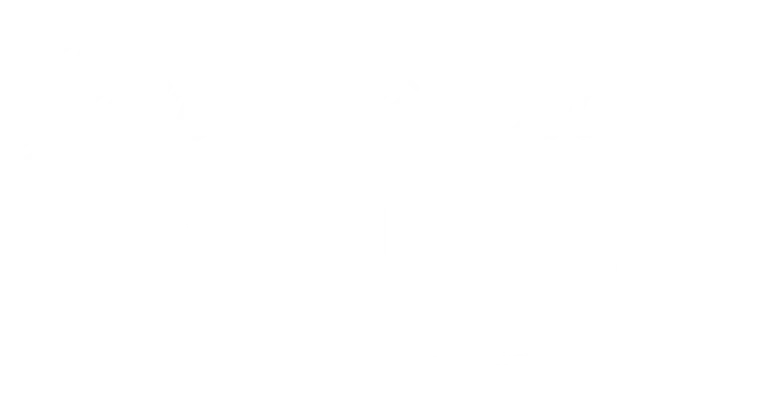
You find these and other figures in my book Happily Ever Cyber and on Cisa.gov

Find out how to push Cybermonsters away from your private data
With tips to help prevent a cyber attack protecting your family, work environment and yourself:
AS SEEN ON:

Find out how to push Cybermonsters away from your private data
With tips to help prevent a cyber attack protecting your family, work environment and yourself:
AS SEEN ON:
Push Cybermonsters away from your private data.
Subscribe to my newsletter about cybersecurity and cyber safety. New issues every Tuesday.

Push Cybermonsters away from your private data.
Subscribe to my newsletter about cybersecurity and cyber safety. New issues every Tuesday.

Protect those that matters most to you:

Family
Protect your child(ren), teens,
and your parents.

Business Owners
Protect your data, your customer's information, your employees,
and your brand!

Yourself
Have peace of mind online!
International Bestselling & Award-Winning Cyber Safety Author
Identity theft & cyber crime can happen to anyone.



Why choosing us?
In a world full of digital distractions, we understand the importance of cultivating a healthy balance. At Way2Protect, our mission is clear: to be your trusted guide to a conscious and protected online experience, both for you and for what you value most: your family, your business, and your peace of mind.
Way2Protect becomes your fundamental ally in your digital world, providing you with hassle-free security and adapting cybersecurity practices to your routine without sacrificing your time. We facilitate the process, guiding you in the implementation of effective cybersecurity practices to protect your family, your business, and your work teams.
Why choosing us?
In a world full of digital distractions, we understand the importance of cultivating a healthy balance. At Way2Protect, our mission is clear: to be your trusted guide to a conscious and protected online experience, both for you and for what you value most: your family, your business, and your peace of mind.
Way2Protect becomes your fundamental ally in your digital world, providing you with hassle-free security and adapting cybersecurity practices to your routine without sacrificing your time. We facilitate the process, guiding you in the implementation of effective cybersecurity practices to protect your family, your business, and your work teams.

Get the latest news in the Cyber Security World
What kind of businesses do Cybermonsters target online?
Imagine you open your computer and you see a message saying: your computer is not available, you must pay the ransom to access your files, your email, and your customer information. What would you do?
You may be thinking, “This could never happen to me!” but in my 20+ years in the Cybersecurity industry, I have witnessed that cyber threats are not only there for the rich, the famous, or the big companies.
From a small local brick and mortar store, a multinational company, or a solo entrepreneur, any business can be at risk! I’ve seen cases involving all industries and incomes. Cybercrime can happen to any size, type, and class of business.
Did you know that a ransom attack occurs every 14 seconds?
Did you know that the estimated damage cost for 2019 was at $11.5 billion?
Did you know that 43% of data breaches occurred to small business and within 6 months 60% of them were out of business?

If your business is online, your business is a target for those looking to threaten your livelihood. I call them Cybermonsters™, because monsters are mythical creatures and many don’t believe in them. Cybermonsters™ are like the monster under the bed or in the closet: elusive, dangerous, and nearly invisible, but these are very real!
Cybermonsters™ have many motivations. Here are a few:
Money. Scammers want to make a profit or some financial gain.
Hackers want to disrupt or bring attention to a specific cause, and desire to embarrass and humiliate your business.
Negatively affect your organization or business operation by misusing the access to your essential data.
All hackers, scammers, and Cybermonsters™ will try to steal these types of valuable information to further their agenda and benefit themselves:
Your customers’ information, like their SSN, ID information, address, phone, email, etc.
Your employees’ financial information, such as retirement plans, 401k, tax records, and other confidential data.
Your business’ intellectual property or trade secrets, which they can use to sell to your competition, or even duplicate your business model!
When I teach businesses, I assure professionals that navigating the vast cyber sea starts with knowing the why, who, and what of cybersecurity. Together, we identify the sensitive information that needs protection, analyze how Cybermonsters™ work, and implement simple steps to improve their business’ cybersecurity and data privacy.
What do YOU do to keep your business safe from cyberthreats? I look forward to teaching you more ways you can safeguard your business against hackers, scammers, and Cybermonsters™.

You may Also like to read :- How to Safely Open An Email Attachment
3 Sure Fire Ways To Find Out If An Email is Safe
Understanding Privacy and Code of Conduct
What is a Data Breach? Understanding the Impact and Prevention
It’s time to protect your loved ones from hackers, scammers, and Cybermonsters! Inner cyber course
Live Happily Ever Cyber!
Sandra Estok
Subscribe for more ways to protect what matters most to you against hackers, scammers, and Cybermonsters™